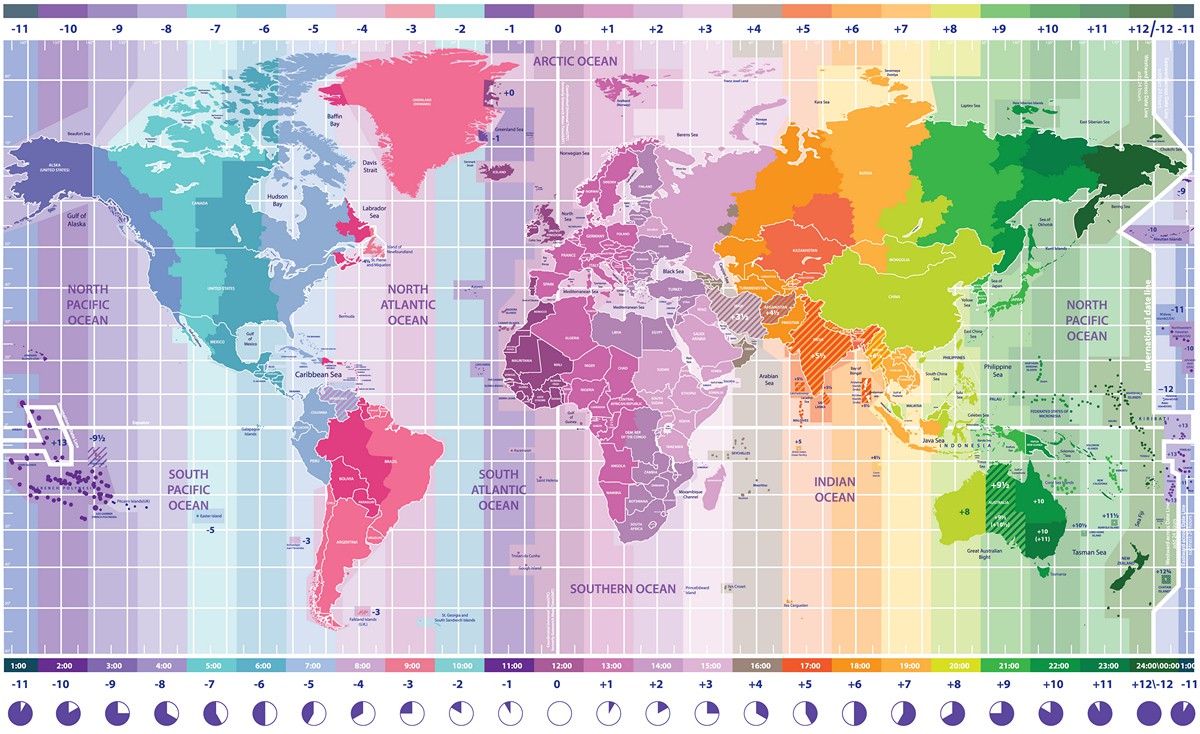
I’ve written about the importance of having accurate time before, and have always said that it can be difficult to keep a proper clock. I’ve always looked at it from a technical standpoint but a couple of days ago, one of my students sent me a video
and it caused me to look at the topic of time from a completely different perspective.
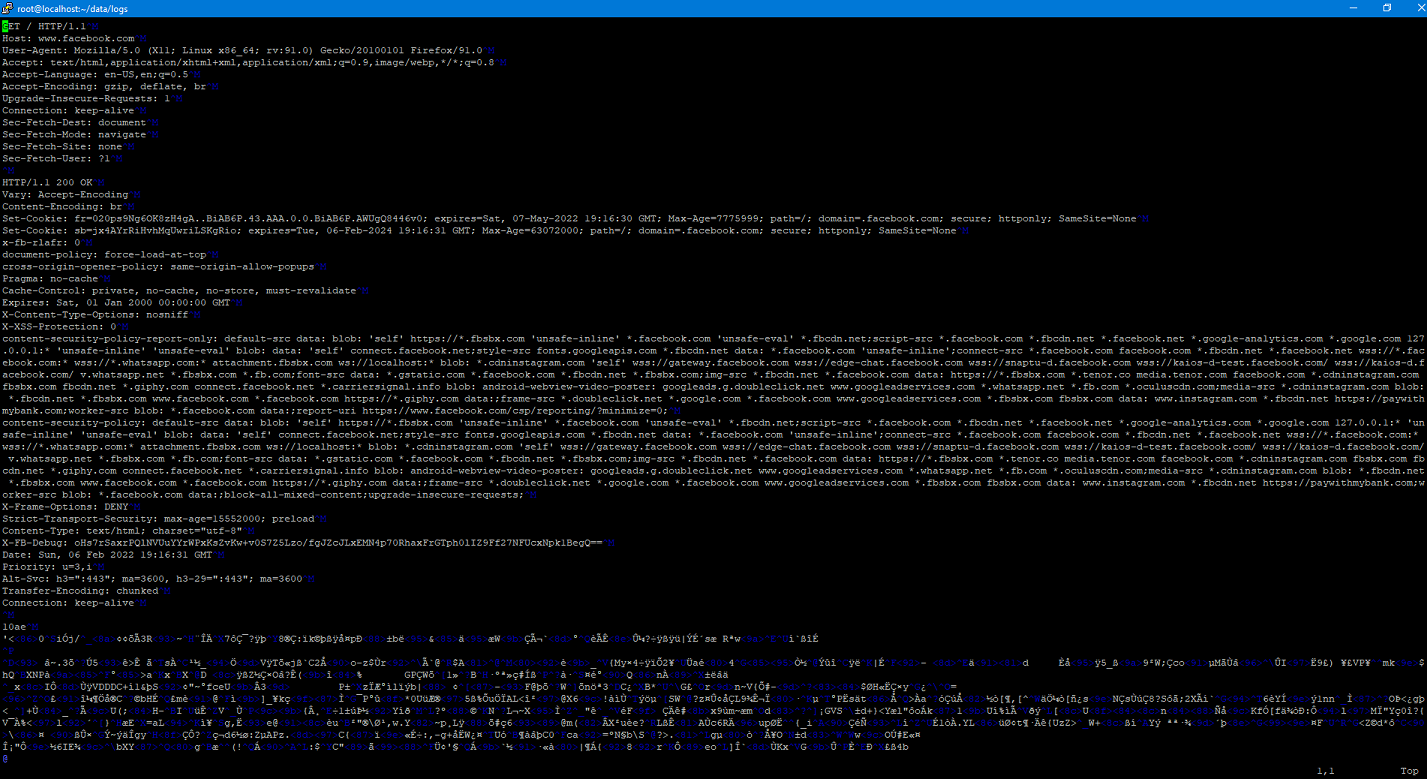
Implementing SSLSplit
A couple of weeks ago I talked about using SSLSplit to at as a proxy so that I could examine the mechanics of a Docker pull. I decided to go ahead a set up a purpose-built VM just for this so I could easily do this again in the future. I wanted to go ahead and document (and share) the steps that I went through for this.
Mechanics of Docker Pull
Recently I’ve been in the process of building an offline repository of software for a project at work. The idea is that we’ll be able to completely install all required software completely disconnected from the Internet. When it got time to deal with containers…challenges abounded.
Unique Identifiers of a Fresh Kali Image
The act of attributing a cyber attack is a long sought after, but rarely attained goal. While things such as techniques, IP addresses, and other artifacts can plan an important role in attributing an attack, being able to attribute actions to a specific computer that has been obtained can help provide overwhelming proof of an act. In this post, I’m publishing a paper that I started working on a few months ago (life gets busy) that provides a forensic analysis of multiple freshly installed Kali systems. My goal over the coming months is to conduct similar experiments on other operating systems. I’ve also provided the raw data that I used to conduct my analysis.