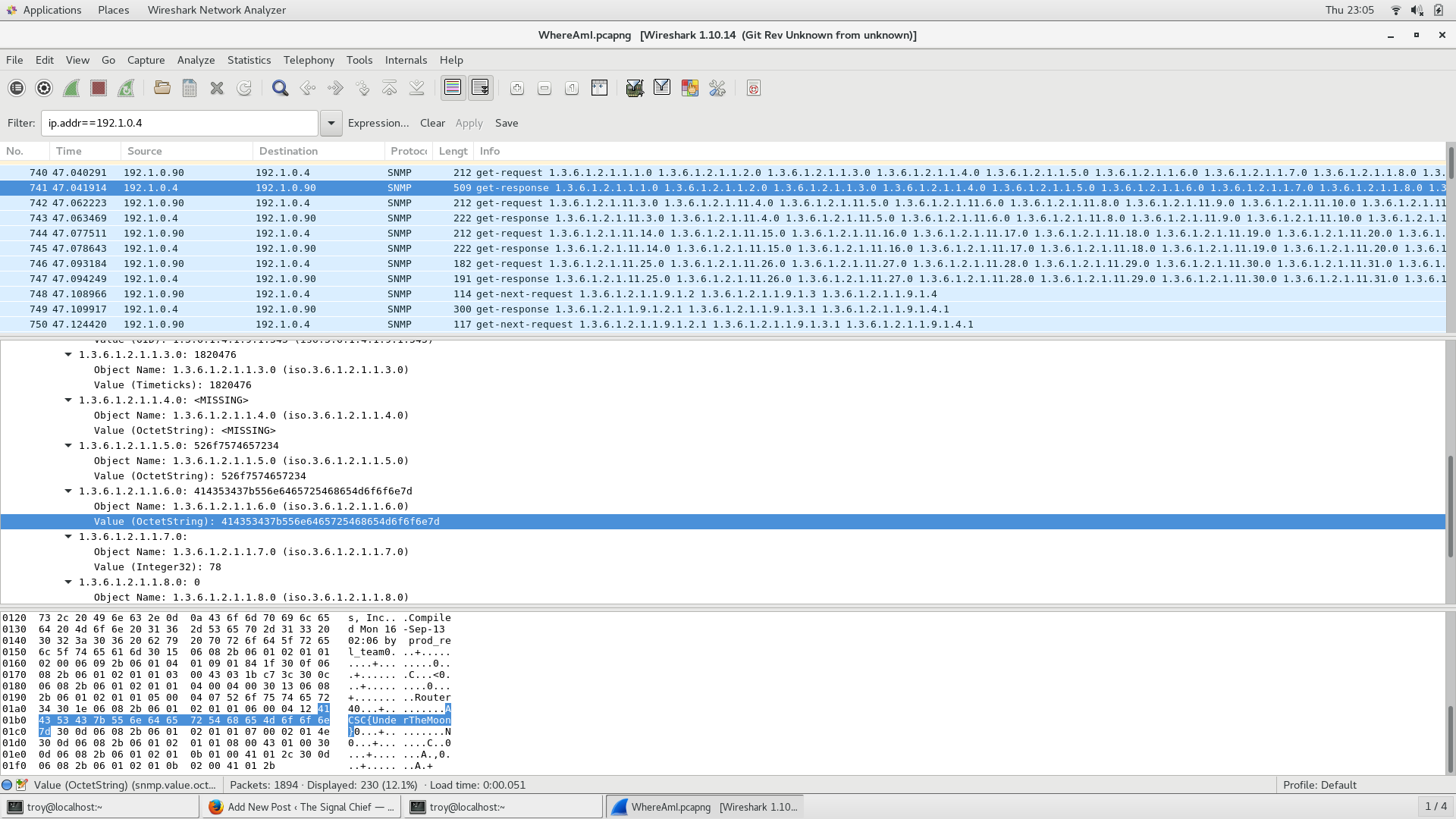
Another problem from ACSC5. You’ve been able to get on a router and capture some traffic in an effort to map out the the corporate network. Your intelligence team has told you that your target device has an IP address of 172.16.58.47 but no one knows that actual location of it. Examine the network traffic and see if you can figure out the location of that device.
animate_me
Yet another problem from ACSC5. Really not much of a clue needed, find the flag
Slow Mover
Another problem from the 5th annual Army Cyber Skills Challenge. The problem is called slow_mover and can be found here.
Problem
Your boss just handed you this PCAP that one of your network sensors captured. He’s positive that there is something fishy going on here but has no clue what it is.
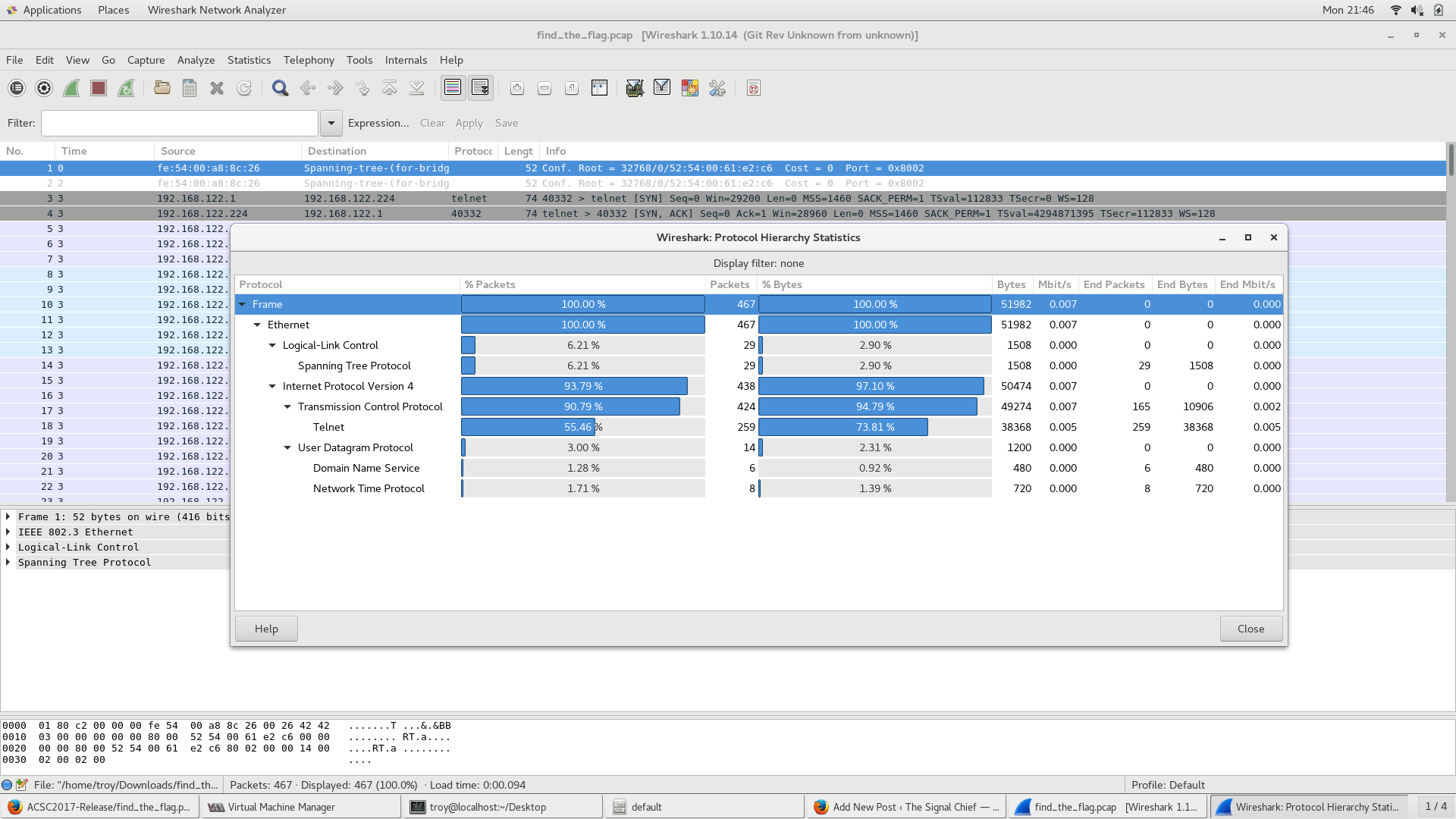
find_the_flag
Another quick walk-through from ACSC5. This problem is called find_the_flag. Problem: Someone thought that using telnet was a good idea. Guess this should make your job a lot easier…..Find the flag
whats_my_password
Another quick walk-through from ACSC5. This problem is called whats_my_password.
Problem
What is that administrator’s password? Note: enter the flag in the format acsc2017{}
find_the_stack2
The is a follow-on to the first find_the_stack problem from ACSC5. This was originally supposed to be the third one in a series of challenges based on this problem but I had some problems with number two so this became number two.
find_the_stack
This is the first of what will hopefully be many walk-throughs from various CTF competitions I’ve competed/worked on. This first challenge is a simple one that I created for the 5th annual Army Cyber Skills Challenge.
Capture the Flags
Many of us remember playing capture the flag (CTF) back when we were kids. The idea was to divide into teams, try to sneak to the other teams side and capture their flag. Years later, this idea was expanded on when Playstation and XBox started putting together multiplayer games that had the same general idea. More recently, the idea has morphed once again with hacking and computer security related CTF competitions. Perhaps the most famous CTF is the annual Defcon CTF where participants from around the world work to qualify to take part in the event at the conference itself, but this is just one of countless CTF competitions that take place on nearly a daily basis.